Platform, Security, Workplace
A blog website to…
Build. Secure. Automate.
Microsoft Intune Endpoint Privilege Management gets more flexible and secure
06/03/2026
Microsoft Intune Endpoint Privilege Management gets more flexible and secure
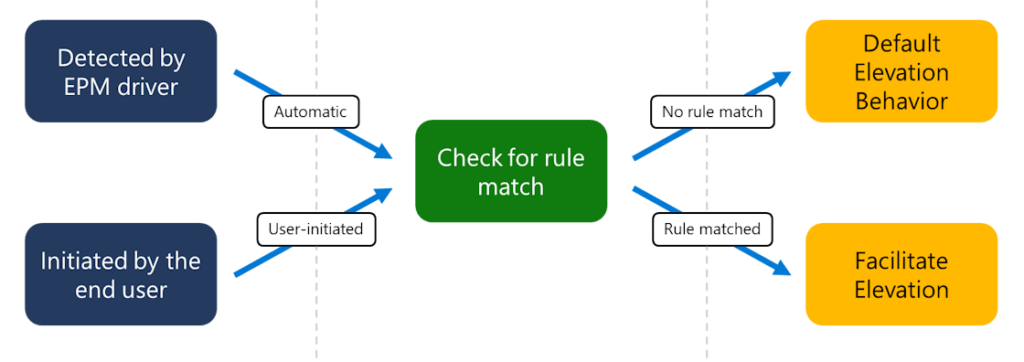
Microsoft continues to strengthen Endpoint Privilege Management in Intune. Two new improvements make privilege elevation more compatible and more secure
The two major updates are:
• Elevate as current user – improved compatibility for installers and applications
• Scope tag enforcement for elevation requests – stronger administrative access control
Together, these updates make EPM more practical for day-to-day endpoint management while maintaining strong security boundaries.
Elevate Applications Using the User’s Own Identity
One of the most common challenges with privilege elevation tools is application compatibility. Previously, Endpoint Privilege Management elevated processes using a virtual account on the device. While this approach improves security isolation, it can cause problems for installers and tools that rely on user-specific resources such as:
• User profile paths
• Environment variables
• Registry keys in HKCU
• Authenticated network resources (such as Kerberos tickets)
To address this, Microsoft introduced the “Elevate as current user” option. With this capability, elevated applications run under the signed-in user’s identity. This gives them full access to the user’s profile context. This change significantly improves compatibility for scenarios like:
• Software installers that depend on user profile paths
• Scripts accessing user-specific registry settings
• Applications that require authenticated access to network resources
• Tools relying on user environment variables
What does this mean?
In practice, this means fewer failed installs and fewer workarounds for administrators managing modern Windows environments. Because this method runs the elevated process under the user’s identity rather than a virtual account, it also increases exposure to user-specific data. For that reason, Microsoft recommends using this option only when necessary for compatibility scenarios, rather than as the default elevation method.
Scope Tag Enforcement for Elevation Requests
The second major update strengthens administrative security within Intune environments that use delegated administration. Starting with the November 2025 Intune service update, Microsoft introduced scope tag enforcement for EPM elevation requests. Scope tags already play an important role in Microsoft Intune by allowing organizations to limit what administrators can see and manage. Now, those same boundaries also apply to privilege elevation workflows. With this improvement:
• Administrators can only view elevation requests for devices and users within their assigned scope tags
• Admin teams cannot accidentally access elevation activity outside their management scope
• Delegated administration becomes more secure and predictable
This aligns closely with Zero Trust principles, ensuring that administrative visibility follows the least-privilege model.
Why This Matters for Modern Endpoint Management
These enhancements make Endpoint Privilege Management significantly more practical for real-world enterprise environments. Organizations benefit from:
• Improved application compatibility without granting permanent admin rights;
• Better control over elevation workflows in large or multi-team environments;
• Stronger separation of administrative responsibilities.
For large enterprises, managed service providers, and organizations with distributed IT teams, scope-based elevation visibility is especially valuable. Each team can manage its own devices and users without exposure to the entire tenant.
Bottom Line
These updates push Endpoint Privilege Management closer to a mature solution. It now better balances security, usability, and administrative control for Zero Trust-aligned organizations.
